Telecoms, data center infrastructure infiltrated, Bloomberg stories say, mystery deepens despite denials

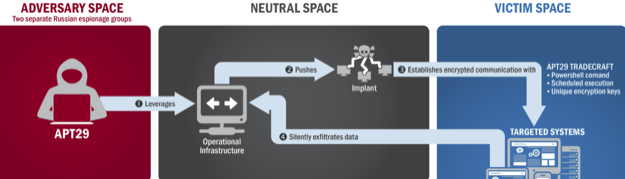
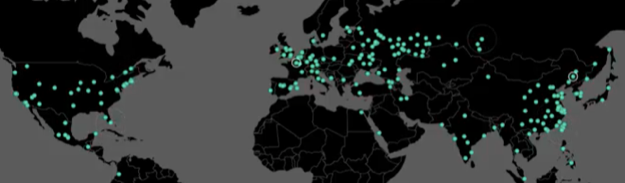
Taken at face value, a pair of articles on Bloomberg by Jordan Robertson and Michael Riley details how Chinese government intelligence agencies snuck tiny chips into computer servers used by Amazon and Apple, and by at least one major U.S. telecoms company. The devices – as small as the tip of a pencil – could be used to listen to communications going in and out, or to dive deeper into those systems.
If true, Bloomberg’s reporting means that the Chinese government, and possibly other intelligence agencies and criminal groups, have a backdoor that leads deep into U.S.… More


![By General Artists Corporation-GAC-management. [Public domain], via Wikimedia Commons](https://www.tellusventure.com/images/2017/3/shoe_phone.jpg)
