FBI’s plea for encryption back doors based on false information
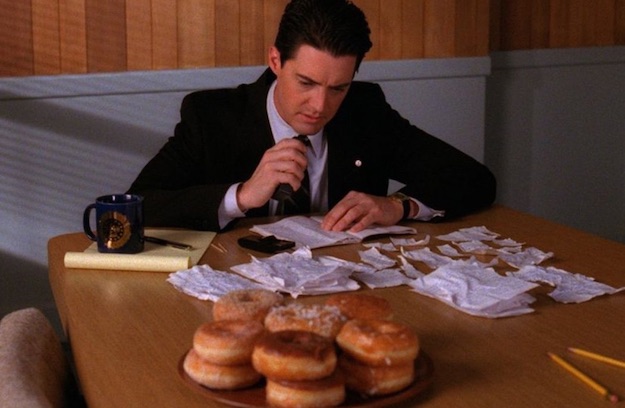
The Federal Bureau of Investigation gave the U.S. congress and the public bad information about the problems it has cracking encrypted phones during investigations, many times over several months. According to a story by Devlin Barrett in the Washington Post, FBI director Christopher Wray repeatedly, and falsely, claimed that agents were locked out of almost 7,800 smart phones and other devices, because of advanced encryption.
He began using the 7,800 figure last year, when he urged congress to give law enforcement back door access to encrypted devices and content…
… MoreWray has repeated the claim about 7,800 locked phones, including in a March speech.



![By FBI (FBI.gov) [Public domain], via Wikimedia Commons](https://www.tellusventure.com/images/2016/4/fbi_anti_piracy.jpg)
![By Billy Hathorn (Own work) [CC BY 3.0 (https://creativecommons.org/licenses/by/3.0)], via Wikimedia Commons](https://www.tellusventure.com/images/2016/2/fbi_building.jpg)
![By Marianah.96 (Own work) [CC BY-SA 4.0 (https://creativecommons.org/licenses/by-sa/4.0)], via Wikimedia Commons](https://www.tellusventure.com/images/2015/7/sample_containers.jpg)